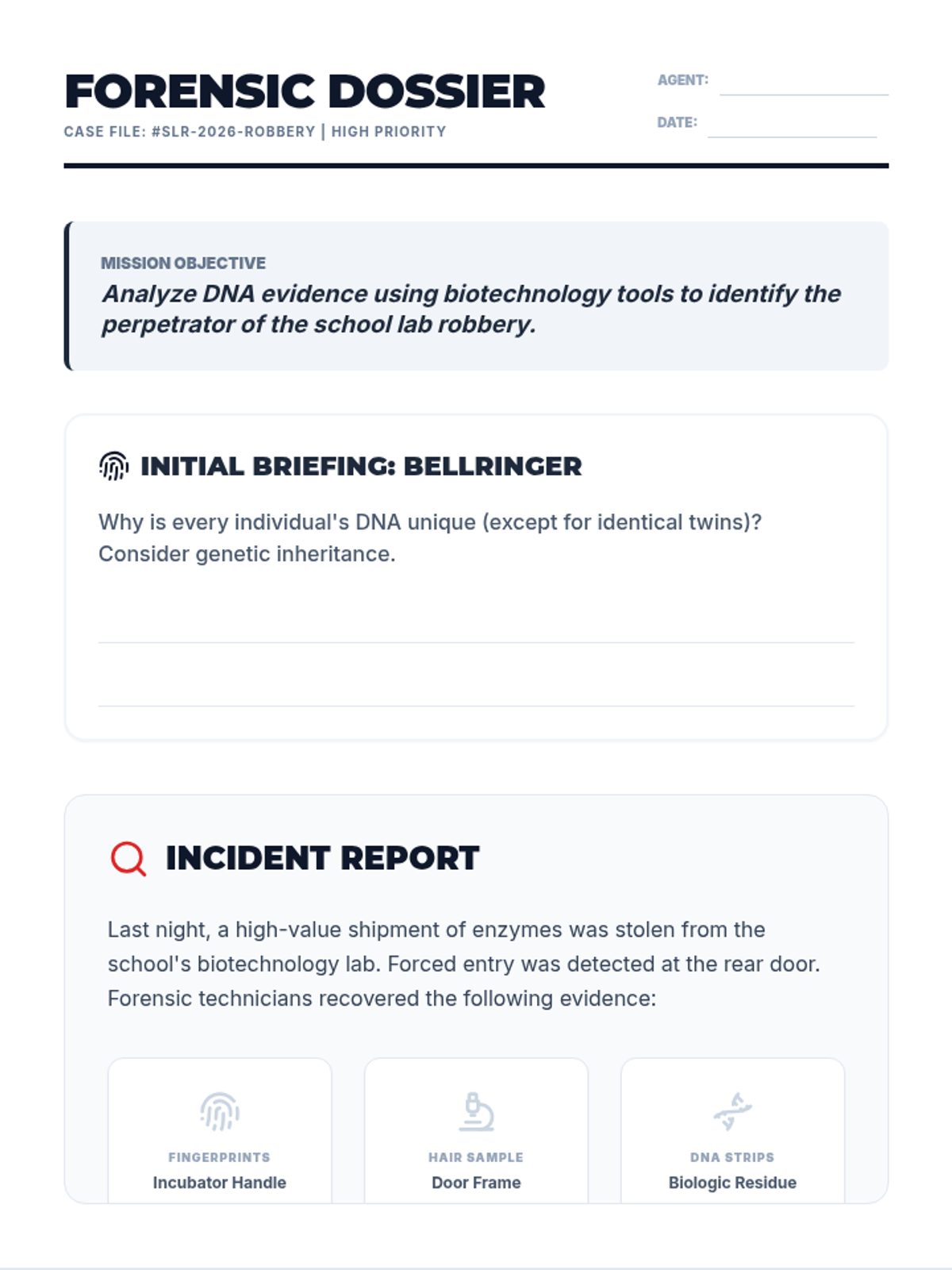
A high-stakes cybersecurity lesson where 12th graders learn to defend networks by configuring firewall rules and investigating suspicious system activity. Students develop action plans for identifying malicious files and processes in a simulated incident response scenario.