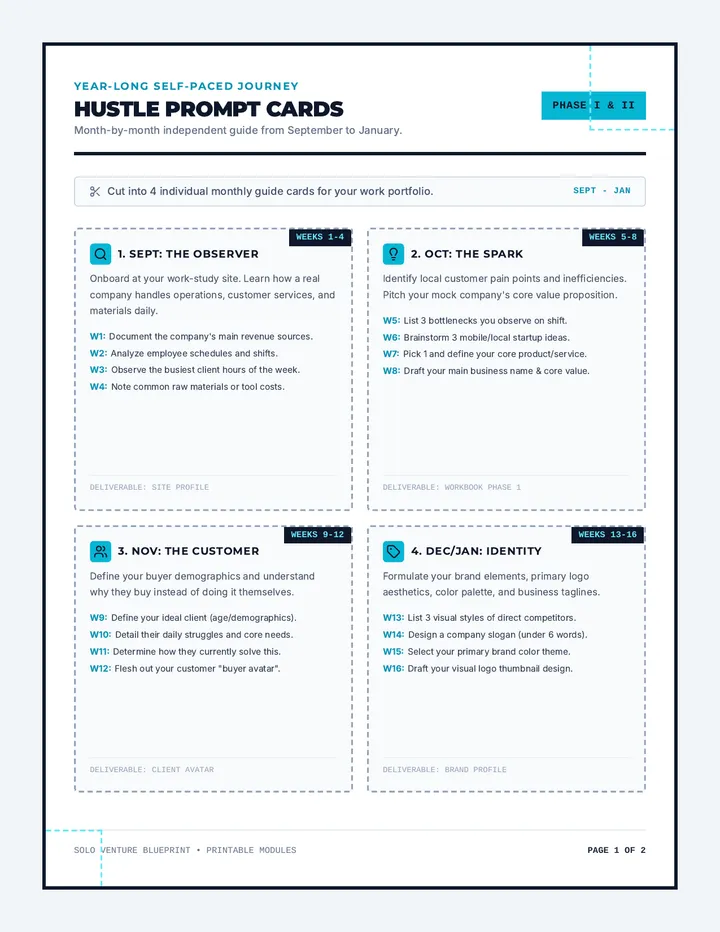
Post Exploitation Privilege Escalation and Lateral Movement
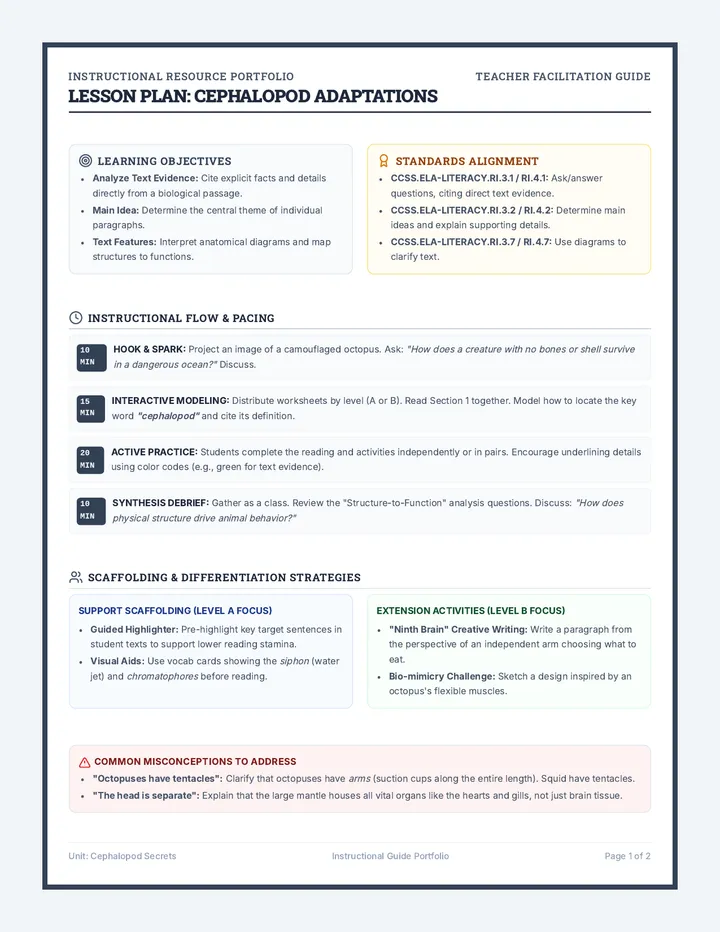
Focusing on post-exploitation, students practice techniques for elevating privileges and pivoting through the network. The lesson covers credential harvesting and 'living off the land' using native system tools.